The store will not work correctly in the case when cookies are disabled.
Stone Insights
-

AMD Ryzen™ AI is a revolutionary technology that brings the power of artificial intelligence (AI) to personal computing. It is integrated into the
Read more
-

Brothers Stephen and James live with their parents, Ellie and Marcus. “Stephen is twelve and has been diagnosed as autistic with selective mutism,
Read more
-

Ten-year-old Nina lives in Norfolk with her parents, Natasha and Daniel, and her four siblings, Sam, Eddie, Andrew, and Roddy.
Nicola says, “My two
Read more
-

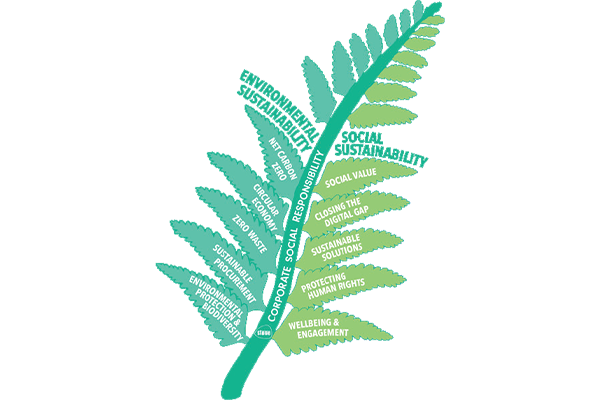
Here at Stone, a Converge Company, we’ve long had the environment at the forefront of our minds.
We hope that our actions – large or small
Read more
-

Aliya and her son Ibrahim live in Darlington. Ibrahim is ten and is on the pathway for an autism diagnosis. The process began four years ago.
Read more
-

Charity is a fundamental part of our business here at Stone, a Converge Company, and 2023 has been a busy year with colleagues and teams taking part
Read more
-

When you turn your laptop on in the morning you expect certain things to happen - lights to glow, fans to hum, the screen to spring to action.
But
Read more
-

Long gone are the days of learning with pen and paper alone. Internet connectivity is now vital to education from primary to secondary and beyond.
Read more
-
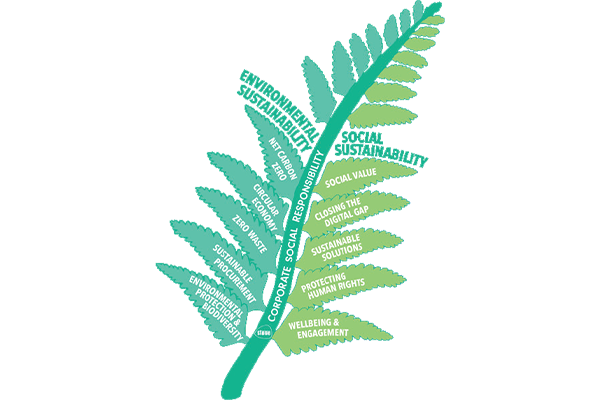
At Stone we believe in a sustainable IT provision offering a full circular economyto meet your needs and delivering innovation with integrity. We can
Read more
-

As companies, consumers, and individuals we all have items around us that we simply don't use anymore. Our habits have changed or we have bought a
Read more